Introduction
As a start to this process, I’ve been following tutorials and understanding some key principles.
- The UE4 client has access to amazon IAM credentials for logging in users via cognito. On Amazon, this IAM credential must be restricted to only cognito logins to not allow someone who has access to this information
- For higher security of data, the unreal server must be the only one to send updates and this should be sent through graphQL/app sync and this must be filtered to only whitelisted IP addresses.
Video
The video I am following for this setup is this video from Lion of of the aws plugin team.
First Step: Setting Up An AWS IAM User Configured to Access Cognito Only.
The first step is setting up a new cognitoOnly amazon AWS user. This is required to allow that user to log in but not access other aws services.
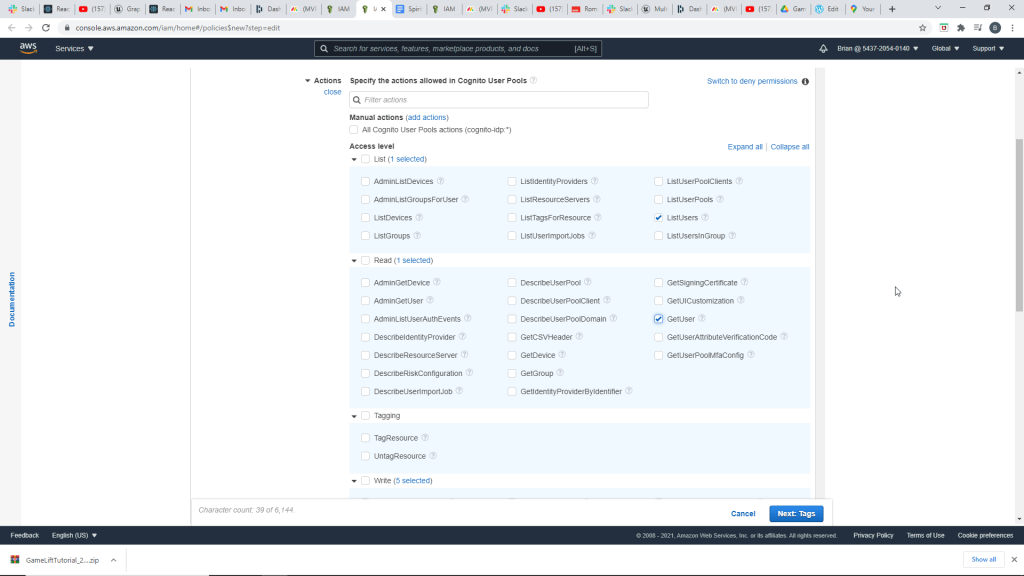
On the policy for this user, we are creating a new policy that restricts access to only certain functions within the CognitoUserPools Service.
This user is restricted to:
SignUp, ConfirmSignup, InitiateAuth, ForgotPassword,ConfirmForgotPassword, ChangePassword, List Users, and Get User

Before finalizing this user, we must create a user pool.
User Pool Creation
The video takes through some standard steps for creating a user pool related to specifications on the user password and email authorization.
The last step gets into some specifics of which app the user pool connects to and options for auth flows configuration.
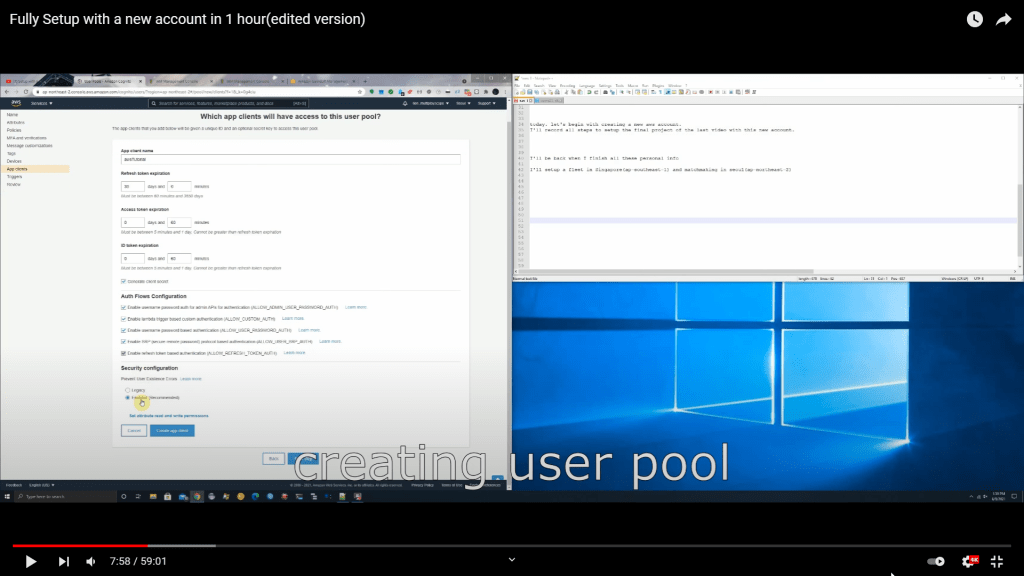
In the video, it is advised that you can generate a client secret here but not to forget to create a secret hash in aws cognito idp’s blueprint nodes.
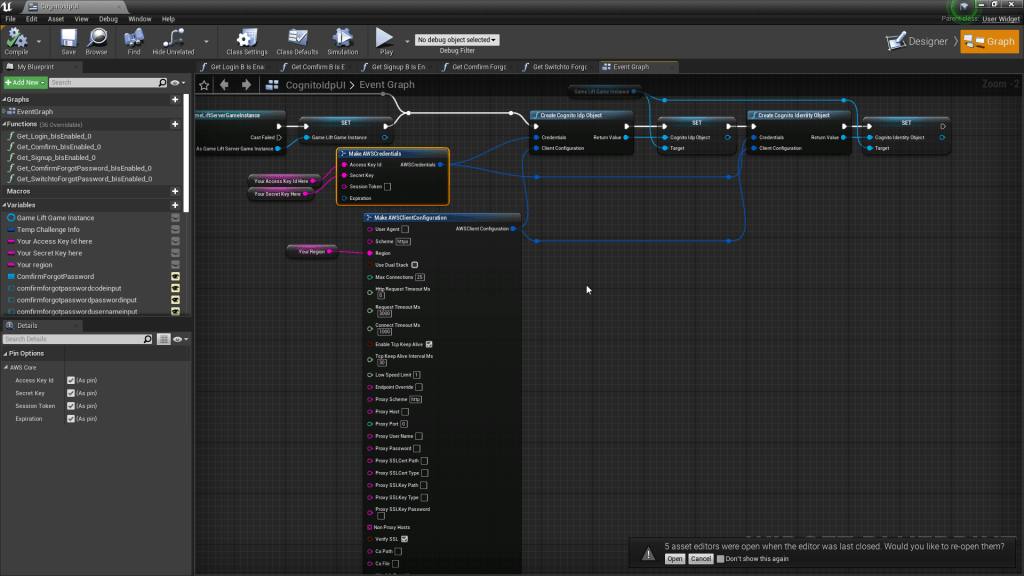
That likely refers to this node here on the cognito only example, we will have to check back on this later.
Adding User Pool Specifics to AWS IAM User Configuration For Cognito Only
The next step involved finishing the IAM user policy to restrict access to only this specific user pool we created. The video shows clicking “Add ARN to Restrict Access” and then shows to copy the region and the specific user pool ID from the user pool you have created.
Configuring Federated Identity Pool
There are some steps to follow to create a federated identity pool. This takes in the User Pool ID and App Client ID.

Adding Cognito Identity Service To Cognito Only AWS IAM User
Add to the policy for the IAM cognito only user access to the Cognito Identity service.
Add only access to getID and GetCredentialsForIdentity.

Now we have enough to finish creating the policy, reviewing the access and naming it cognito_user.
Create an IAM user with this policy
The next step is creating a new IAM user, attaching only this policy. These credentials can now be used inside the ue4 build.
Creating an Admin IAM User.
The video shows steps to create an IAM admin user for use with aws cli.
The video then shows configuring the aws cli to use these credentials, but this part is not completely clear.
Next it looks like it is referencing a role on AWS IAM of Cognito_awstutorialAuthRole. I do not remember seeing this setup earlier in the video.
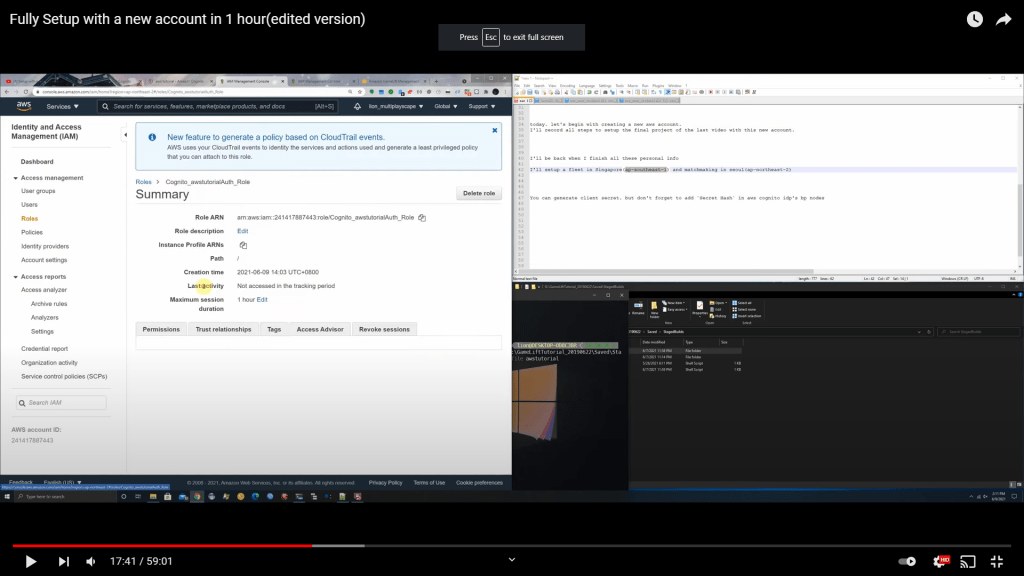
Reviewing what was set up previously, I believe I set this up to be tied to this particular role Cognito_IDPoolFranckStagingAuth_Role, that must have been set up earlier when setting up the user, the policy, and linking the user to the userPool.
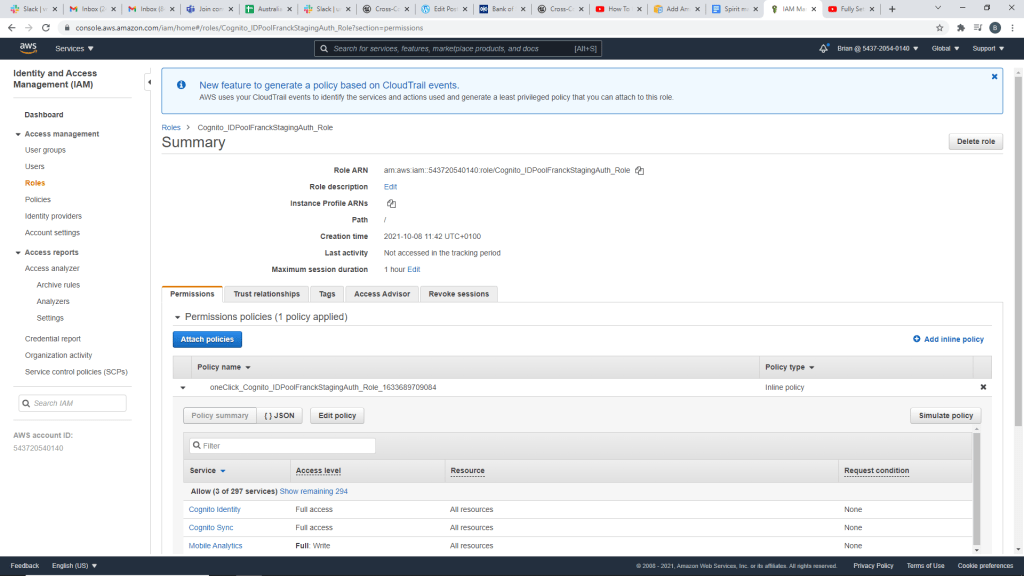
I can see when looking at the trust relationships tab it fits with what I had configured.
Adding Additional Access Permissions to the Authenticated Role
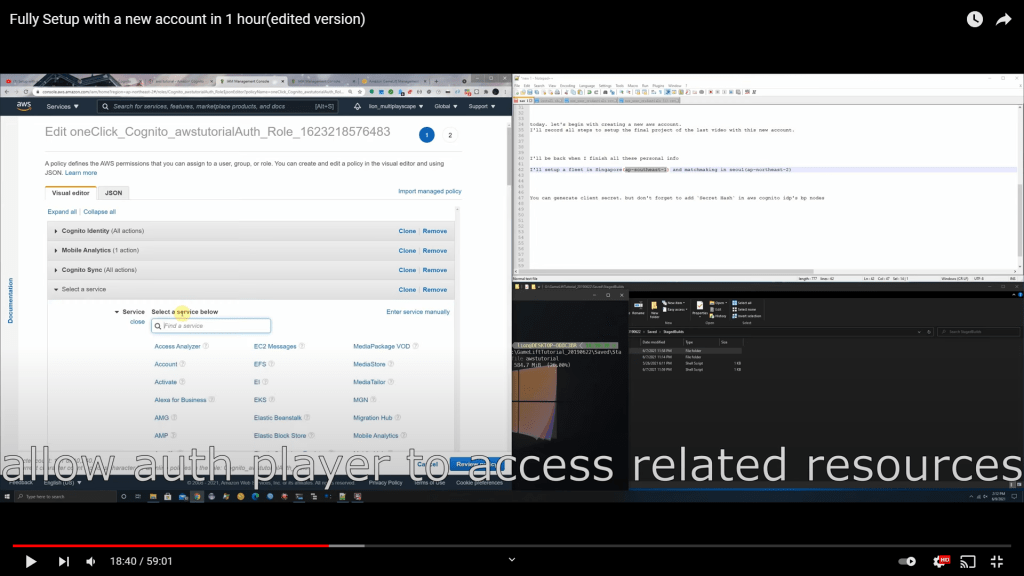
This next step shows adding additional permissions to the authenticated player.
First there is Gamelift & Allow All Gamelift Actions
Then there is Lambda and all Lambda Actions/Resources (this seems potentially dangerous, we may likely have to revisit it).
Then the video briefly showed AppSync but did not add it here.
Setting Up Matchmaking Logic
The tutorial video shows assigning a matchmaking rule set as part of the gamelift setup. We currently do not have that configured.
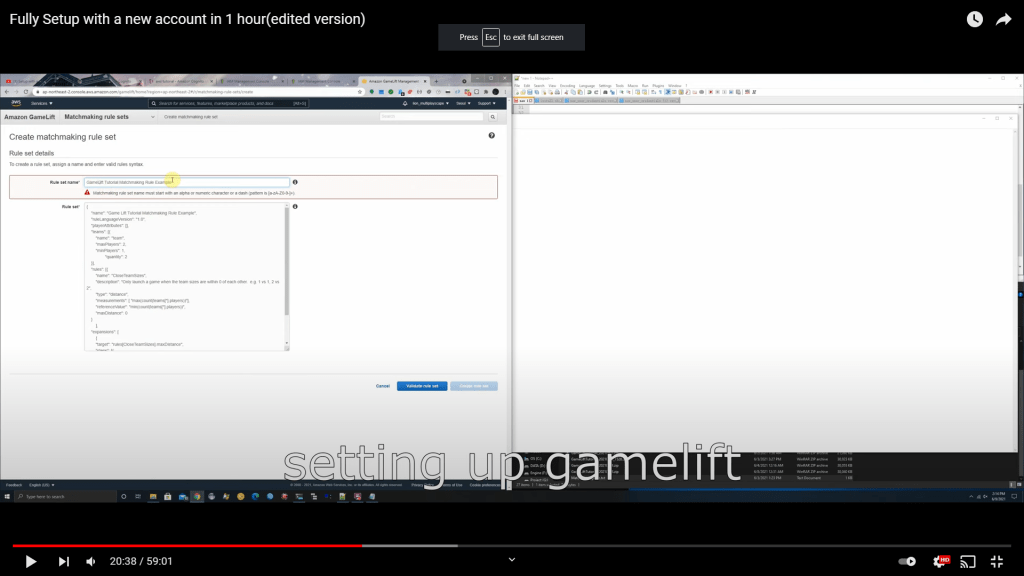
I also found that the eu-west2 region does not support matchmaking, so similar to the example in this video, we will need to assign a different region for matchmaking vs our fleet’s region.
On the description of this video, it mentions:
prerequisites: I have setup the whole matchmaking system in my previous videos, if you want to know how to set up matchmaking systems, please watch my previous videos.
So it seems like I will need to learn more about matchmaking before proceeding further on this tutorial.
This video seems to cover matchmaking from the plugin perspective.
And this starts to cover matchmaking from the official gamelift side.
https://docs.aws.amazon.com/gamelift/latest/flexmatchguide/match-intro.html
Shifting to a new Tutorial to do the original tutorial!
Before diving into another 50 minute long silent tutorial, I felt like it might be helpful to learn from some official aws documentation first.
https://explore.skillbuilder.aws/learn/course/421/play/1224/amazon-gamelift-primer
The primer first describes matchmaking as a pre-requisite, then gets into game session placement.
After a match is found, the game session needs to be started somewhere. Finding the best location available for the game session is called game session placement. The game hosting service should be able to examine the infrastructure resources and select a location that has the lowest average latency for all the players. Game session placement is another game hosting requirement.
The four layers of Gamelift:
Matchmaking relates players that want to play a game with a game session where it can be played.
Game Session Placement figures out where to host game sessions.
Session Management starts games and facilitates players to join games.
And Infrastructure management provides elastic control over game servers.
Notes from team conversation :
Many different types of authenticators/authentications, can be applied to each specific lambda functions.
Can have several entry points that can trigger the same function.
Fetching user profile can be available for web front end or available for a different policy
Settings are very flexible
yml function can regenerate entire aws setup
Different authorizers can be set up per lambda function
get token from launcher, attach token to every api request

Leave a comment